SSH tunneling or also known as port forwarding is a way of forwarding normally insecure TCP traffic through SSH. Common ports for example POP3,SMTP,HTTP and FTP can be easily tunneled using SSH.
SSH tunneling is also sometimes used to bypass firewalls where certain ports are blocked.
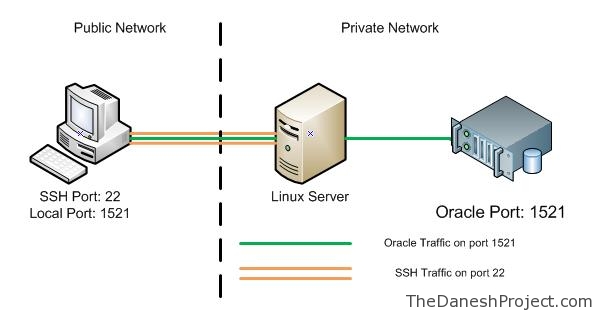
The figure below represents the network setup at my workplace where the only port available to use is SSH port 22. By implementing portwarding over ssh I am able to port forward Oracle traffic over port 22 to my Oracle DB database running on my private VM with host only networking enabled.
In this post I will show you how to apply SSH tunneling using the windows SSH client Putty. I’ll cover the Linux implementation in my future post.
You will need Putty to get started. Putty is a popular free win32 based SSH/Telnet client. Obtain the latest version 0.59 at the homepage.
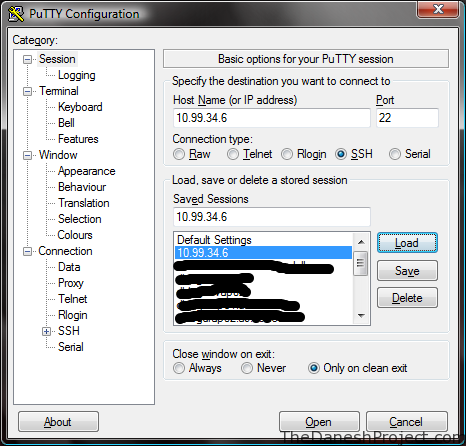
Run Putty, key in the address for your Linux box. In this example “10.99.34.6” “Pandora” is the Linux box hosting VM and on the VM “192.168.66.100” the is an Oracle database running on RHEL 3. The VM is setup with host only networking so it has no access beyond the host machine “Pandora”.
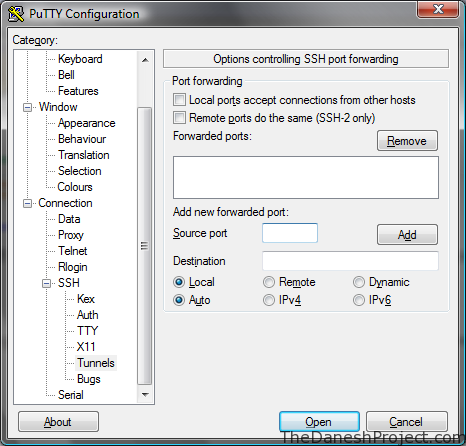
Look for the SSH tree entry in the menu to the left. Expand it and go to “Tunnels”.
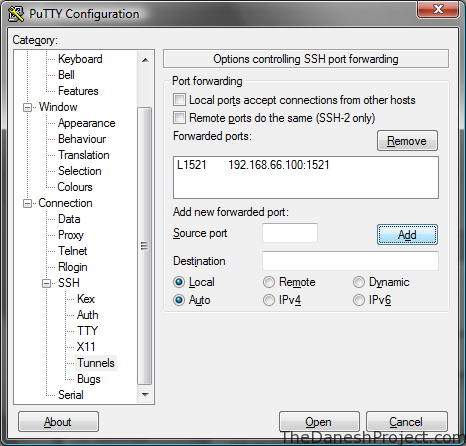
Fill the the required information and click add.
Source Port: 1521
Destination: 192.168.66.100:1521
“Source port” is the port Putty will listen on for incoming connections.
“Destination” is the destination port we are trying to access. In this example the Oracle listener is listening on port 1521 for incoming traffic so we use that.
“1521” is the standard Oracle listener port.
Remember to save the session in the session page.
Open Putty and login to the Linux box “Pandora” and port forwarding should be up.
That’s it, have fun.